Tune Plesk to Meet PCI DSS on Windows¶
This section describes the steps that you should perform if you want to secure your server and achieve compliance with PCI DSS on a Microsoft Windows-based server.
Warning
We highly recommend that you configure the Windows firewall in the server operating system to block all remote procedure calls (RPC) and communications to the Windows Management Instrumentation (WMI) services.
Securing Remote Desktop connections¶
Set up encryption of the remote desktop connections to prevent man-in-the-middle attacks. For instructions, refer to http://technet.microsoft.com/en-us/library/cc782610.aspx.
Changing Remote Desktop connections port¶
Some PCI scanners report a man-in-the-middle attack if you do not change the RDP port to a custom value. To do it, complete the following steps:
Run the
regeditutility by clicking Start > Run, typing regedit, and then clicking OK.Change the port value by modifying the following registry key:
HKEY_LOCAL_MACHINESystemCurrentControlSetControlTerminalServerWinStationsRDP-TcpPortNumber
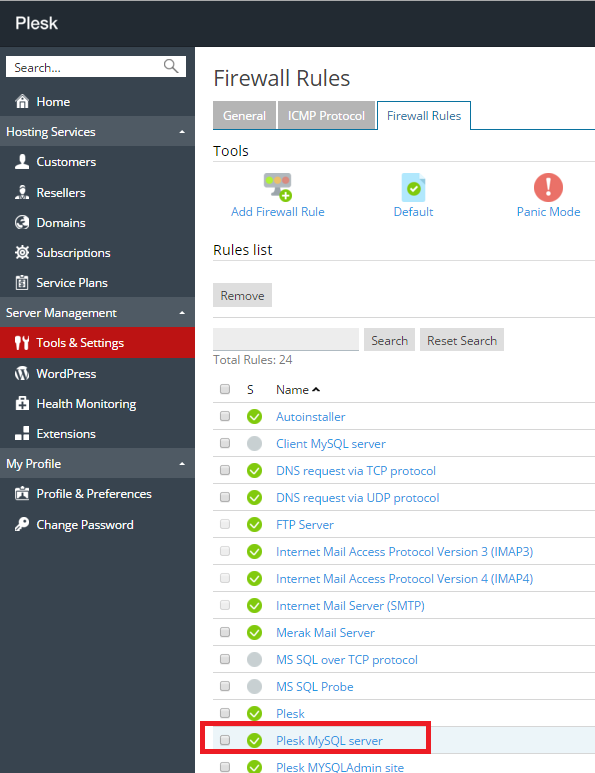
Prohibiting access to MySQL database server from external addresses¶
Use the firewall functions built into your Plesk.
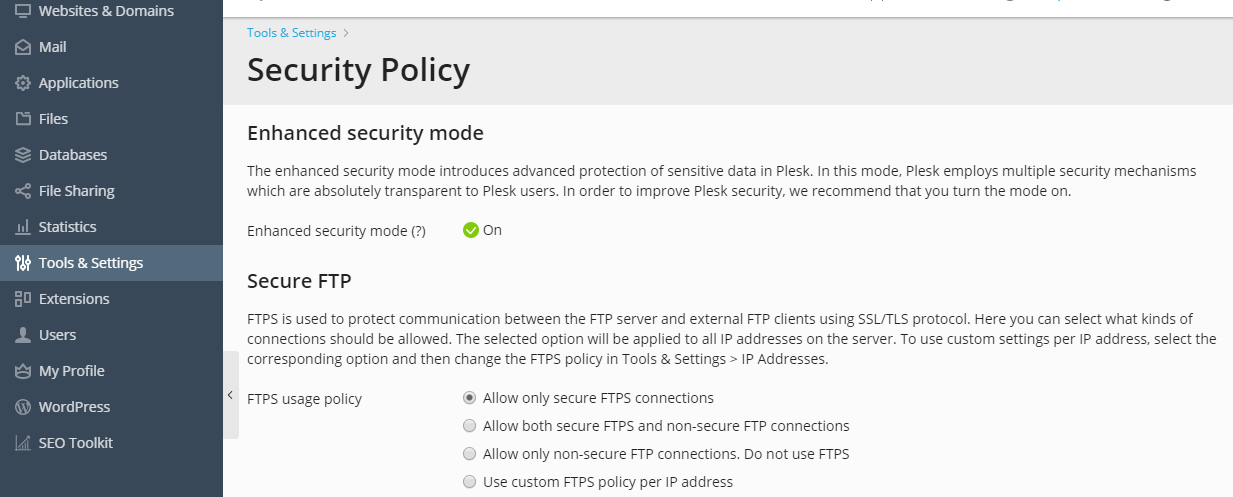
Securing FTP connections¶
If you allow FTP connections to your server, you must prohibit all FTP connections except secure FTPS connections.
To allow only FTPS connections to your server: